Published Dec 18, 2025, 10:30 AM EST
Kanika began writing about consumer technology in 2019 and has contributed to tech websites like Beebom and The Mac Observer. During her journey, she covered a wide range of topics, including Android, Windows, AI, and everything Apple. She has been a loyal iPhone user since 2014, and owns an Apple device from almost every lineup. With a keen eye on the latest trends, she strives to help users get the most out of their gadgets.
Beyond her love for writing, she is a deep researcher and a lifelong learner, always eager to explore the latest innovations and emerging technologies. With her passion for technology and writing, she joined MUO in 2025 as a Freelance Tech Writer.
When not writing, she's probably trying a viral Instagram recipe or watching some thriller suspense on Netflix.
We all know that we shouldn’t click on suspicious links or download files from shady sources because they might contain malware. However, there’s a far more dangerous threat that most people ignore: browser permission pop-ups. We’ve all come across common pop-ups, such as “allow location access” and “allow automatic downloads." Often, these prompts appear on legitimate-looking websites and seem harmless, so it’s common for people to hit the Allow button.
Unfortunately, one wrong click can give websites long-term access to your device and your data. In most cases, wrong browser permissions are more dangerous than malware because you grant permissions by choice, and browsers trust them by their design. If you never really cared about these pop-ups, it’s high time you start caring now and remove any unwanted permissions.
Browser permissions that cause the most damage
Those abused pop-ups
All browser permissions aren’t the same. While some might offer minor inconveniences like push notifications, others can open the door to some serious security, privacy, and usability issues.
Below are some of the most abused browser permissions.
Notification permissions
These pop-ups may seem an innocent way to display useful desktop alerts and push notifications. However, if you grant this permission to a malicious website, it can push scam ads, fake virus alerts, clean-up required alerts, and more. They can even redirect you to phishing pages or annoy you with endless clickbait and fake giveaways. Since these notifications come from your web browser, they might feel trustworthy, which makes it easier for a user to fall for them.
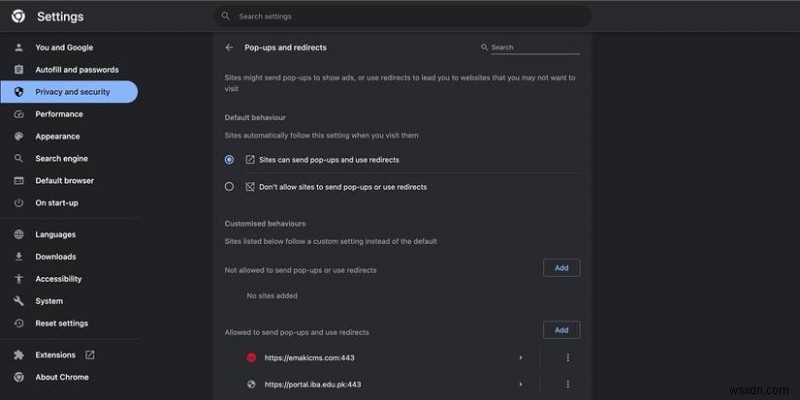
Pop-ups, redirects, and automatic downloads
Some websites may ask your permission to open new browser windows, redirect pages automatically, or download files without any manual intervention. When you grant these permissions, it can cause forced redirects to adult sites, unwanted downloads that clutter your system, or even the delivery of viruses. If you allow these, even the most private web browsers might struggle to protect you.
Clipboard access
This might sound harmless, but it’s not. When you allow a website to access your clipboard, it can read from and write to your clipboard. Now, since your clipboard might have passwords, sensitive information, and financial details, this permission poses a major risk. Malicious websites can read this information, modify your copied links, and do a lot more without even informing you.
Location access
When you give your location access, websites can pinpoint your exact physical location. Sure, location access is useful for navigation apps, local search engines, and weather apps, but some websites request your location data without any genuine reason. If you grant this permission to an untrusted website, it can track your city, daily patterns, or home and workplace location. Malicious websites can continue to track your location even if you aren’t using them actively.
Camera and microphone access
This is something that has to be taken very seriously. When allowed, a website can access your microphone and camera in the background. Record your audio or video and spy on your meetings without your full knowledge, which poses a major surveillance risk. While most major browsers indicate when your microphone or camera is active, some don’t know or notice what triggered them.
Screen or desktop capture
This allows a website or browser extension to capture your screen, which might accidentally expose your private or confidential information. It’s common for a recording or screen-sharing app to ask for this permission, but you should make sure that you aren’t allowing any unknown or untrusted website to capture your screen.
These permissions are clear examples of how a single careless click can put your privacy and security at risk.
Why browser permissions are more dangerous than malware
Because you’re granting them
Let’s face it. We are all aware of malware, adware, and viruses. We are conditioned to fear it and try to take precautions to avoid it. On the other hand, browser permissions feel harmless and official. And that’s where the problem is. Malware tries to break in, whereas browser permissions are given by your choice. Once you allow something, your browser will trust those websites, and the permissions persist until you revoke them manually.
Unlike malware, browser permissions are applied across sessions, sync across your devices, and don’t trigger any security alerts. It’s worth knowing that malicious websites no longer rely on technical exploits. All they need is a convincing prompt. Most of us don’t pay close attention to these pop-ups, which makes it easier for websites to take our permission and target us with scams and unwanted redirects.
That said, not all permissions are misused. It’s safe to click the “Allow” button when you frequently visit a website you trust and it clearly explains why it needs the access. It also makes sense for a website to ask for your permission when you’ve requested a particular feature. For instance, a website may ask for camera and microphone access if you want to make a video call.
How to check and remove unwanted permissions
Revoke access in minutes
You may feel that it’s complicated and tedious to check and clean up permissions on your device. Fortunately, it’s exactly the opposite. It’s easier, quicker, and one of the best security upgrades you’ll ever make. All major web browsers offer simple ways to check and review permissions.
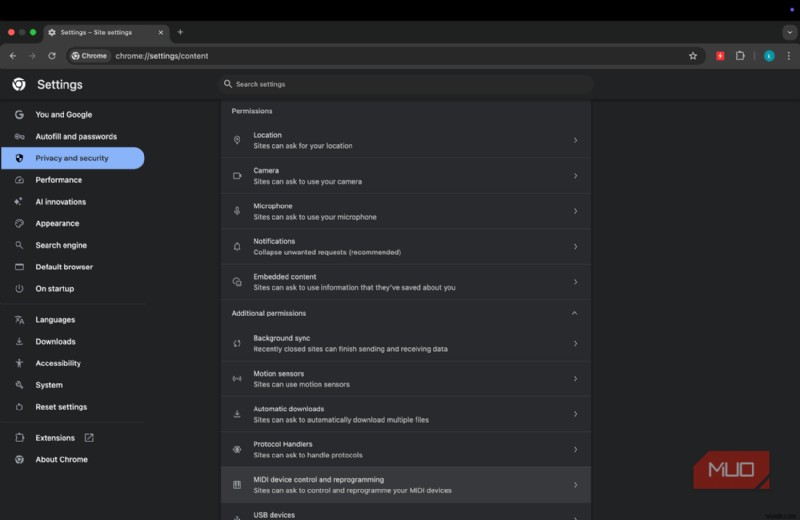
- If you’re using Chrome or Edge browsers, go to Settings.
- Choose Privacy and Security from the left panel.
- From the bottom, click on Site Settings.
- From here, you can review your permissions like location, camera, microphone, and notifications. You should disable or block any permissions that you don’t recognize or use.
- You can also review your recent activity to check which websites have been blocked or allowed a particular permission.
While reviewing permissions on my browser, I’ve blocked notifications and automatic downloads pop-ups entirely. For camera, microphone, and location, I’ve chosen the “ask every time” option. You can figure out what works best for you and then make the tweaks accordingly.
 Related
Related
Don’t Tap That Notification—This Is How Malware Sneaks Onto Smartphones
Malware isn't just for computers; protect your phone by understanding the biggest threats.
Don’t allow browser threats to sneak in through permission pop-ups
Of course, malware still exists, but some of the biggest browser threats might walk in through permission pop-ups that you rarely pay attention to. Notification spam, force redirects, silent tracking, and unwanted downloads all exist because a user casually clicks Allow without even thinking. The good news is that it’s pretty simple to fix the problem before the real damage is done. First and foremost, be very skeptical of permission requests, read everything carefully, and grant access only when it makes sense. Also, don’t forget to audit your permissions regularly.
