Published Feb 25, 2026, 2:30 PM EST
Afam's experience in tech publishing dates back to 2018, when he worked for Make Tech Easier. Over the years, he has built a reputation for publishing high-quality guides, reviews, tips, and explainer articles, covering Windows, Linux, and open source tools. His work has been featured on top websites, including Technical Ustad, Windows Report, Guiding Tech, Alphr, and Next of Windows.
He holds a first degree in Computer Science and is a strong advocate for data privacy and security, with several tips, videos, and tutorials on the subject published on the Fuzo Tech YouTube channel.
When he is not working, he loves to spend time with his family, cycling, or tending to his garden.
If you want to pick a VPN provider today, you will probably be confused about which one of the many to choose. On paper, they are all very impressive; from kill switches and advanced protocols down to extensive server networks, there are so many features to consider. But the one feature I consider most important is multi-hop.
Even though a single-hop VPN will encrypt your data, today a sophisticated observer will still be able to piece things together. Multi-hop means your data or traffic is routed through multiple servers in sequence. This creates a chain where no one server sees both your identity and your destination. There are VPNs that I will never trust again, but among those I still use, this feature is a must.
Multi-hop separates identity from traffic end-to-end
No single server holds the full picture
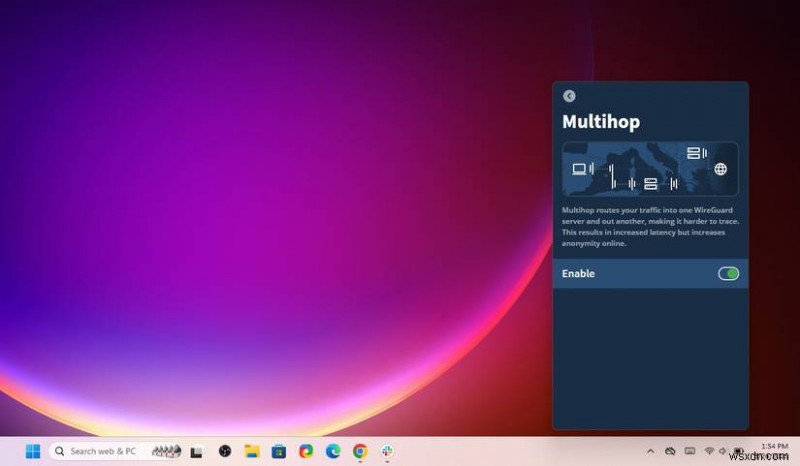
Multi-hop VPNs are also known as cascading or double VPNs. They are structurally similar to the Tor network, routing connections through multiple servers, so no server sees both the origin and destination. This design is essential in protecting identity even in extreme situations when a VPN provider or server is compromised.
It's a different architecture from single-hop VPNs, where a single server may log both the origin and destination. However, the threat is more than breaches and security flaws. There have been cases where VPNs have been legally obligated to hand over information, and a multi-hop chain is still capable of keeping your IP and activity hidden. It's a kind of security infrastructure that doesn't solely rely on a single provider. Information is shared across several points, without any one holding the full context.
One of the reasons why I will always use multi-hop VPNs is that they do not assume that any provider is trustworthy. They assume adversaries may try to correlate traffic across the network. These are the assumptions that make single-hop VPNs seriously flawed. Any observer trying to trace traffic on a double VPN will get fragments, and even the timing patterns are significantly harder to analyze. It's a kind of VPN that creates distributed trust redundancy.
Adversaries capable of observing traffic end-to-end
Metadata analysis doesn’t require breaking encryption
There are several levels of eavesdroppers on the internet. An ISP logging traffic is one case; nation-state monitoring is a far more powerful adversary. Observers do not always have to break encryption to reveal identities if they can correlate timing, analyze packet sizes, and observe traffic patterns. You have little defense against such actors if you use a single-hop VPN.
The reason why multi-hop disrupts correlation attacks is that it uses geographically and jurisdictionally separated servers to isolate entry and exit points. Once traffic arrives at the second server, any obvious link to the original IP is obscured. It becomes exponentially harder for an adversary who may have control over one of the servers to correlate traffic back to the original user. Among commercially available VPN configurations, multi-hop is sometimes the only possible setup that offers any meaningful protection.
Provider choices and server trust matter more than ever
Jurisdiction, infrastructure, and legal exposure
While multi-hop is essential, there's more to consider before trusting your connection to any double VPN provider. Some providers implement this feature by chaining two servers that they control within the same jurisdiction. Technically, you will be getting the multi-hop benefits, but you have very little legal or operational protection. A dynamic multi-hop setup where servers cut across independent providers and jurisdictions matters even more.
If your provider's servers are in Five Eyes countries — Australia, Canada, New Zealand, the United Kingdom, and the United States — you are more vulnerable to coordinated legal or intelligence requests. Ideally, multi-hop setups should span multiple legal jurisdictions or allow you to create or select hops. These kinds of setups make penetration harder.
Based on these points, there are certain VPNs I trust and others that I would rather stay clear of. I have listed my personal preferences in the table below:
Provider
Multi-hop name
Server control
Jurisdiction of provider
Hop countries
User control over hop selection
Dynamic or static
Five Eyes exposure
Mullvad
Multi-hop
Single provider (own servers) and high-quality rented (leased) servers
Sweden (EU/GDPR)
49 countries
Full (choose any entry and exit)
Dynamic
No
Obscura VPN + Mullvad
Two-party VPN
Two independent providers
Obscura: US; Mullvad: Sweden
Separate jurisdictions by design
Limited (Mullvad handles exit)
Static architecture
Obscura is US-based
ProtonVPN
Secure Core
Single provider (own servers)
Switzerland
Entry locked to Iceland, Switzerland, or Sweden; exit is user's choice
Partial (exit is flexible, entry is fixed)
Partially dynamic
No
NordVPN
Double VPN
Single provider (own servers)
Panama (parent company: Netherlands)
Fixed server pairs — limited country combinations
Minimal (pre-configured pairs only)
Static
No (Panama), but parent company in Netherlands (14 Eyes adjacent)
IVPN
Multi-hop
Single provider (self-hosted servers) and high-quality rented (leased) servers
Gibraltar
Multiple countries; entry and exit must be in different countries
Full (any entry/exit combination)
Dynamic
No
Multi-hop is the feature I now filter every VPN through
If you choose multi-hop, you should know that traffic will have to travel farther and probably pass through additional encryption, which can cause some latency. In practical terms, you are adding about 20 to 60 extra seconds to requests.
Whatever latency it may cause, it is a fair trade-off for that extra layer of security and privacy. So, one way I guarantee I'm not using my VPN wrong is by starting off with one that has the multi-hop feature.
 Related
Related
Is Using Two VPNs Better? No—Here’s Why
Double could spell trouble when using more than one VPN.
