Author: Konstantinos Tsoukalas , Last updated: April 7th, 2026
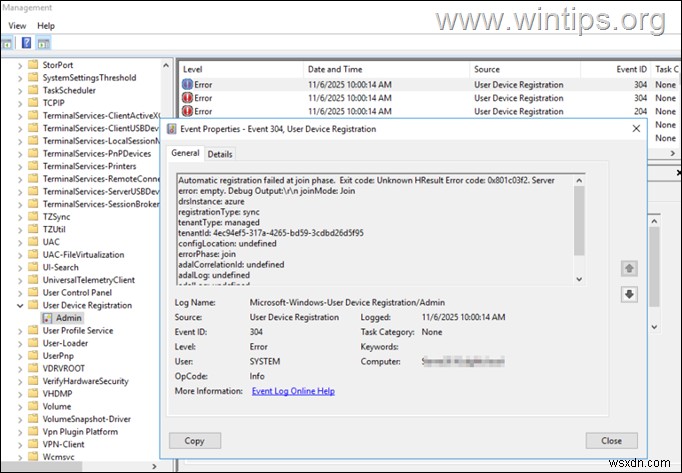
If you're trying to enroll/join a device to Microsoft Entra ID/Intune and you receiving the "User Device Registration – Event ID's 304 & 307" with error "Automatic registration failed at join phase", continue below to fix the problem.
The error "Automatic registration failed at join phase. Exit code: Unknown HResult Error code: 0x801c03f2”, typically occurs when Intune Auto Device Enrollment is disabled. In other cases, in Microsoft Entra Hybrid Join implementations, the error occurs when the specified Azure AD login account does not have sufficient access rights to perform the synchronization or when the domain user(s) trying to register/enroll their device with Microsoft Entra/Intune has incorrect rights.
In this guide you will find step-by-step instructions to fix the following errors in "Event Viewer > Applications and Services Logs > Microsoft > Windows >User Device Registration > Admin":
- Log Name: Microsoft-Windows-User Device Registration/Admin
Source: Microsoft-Windows-User Device Registration
Event ID: 304
Error Description: Automatic registration failed at join phase. Exit code: Unknown HResult Error code: 0x801c001d. Server error:. Debug Output:\r\n undefined - Log Name: Microsoft-Windows-User Device Registration/Admin
Source: User Device Registration
Event ID: 307
Error Description: Automatic registration failed. Failed to lookup the registration service information from Active Directory. Exit code: Unknown HResult Error code: 0x801c001d.
How to fix User Device Registration Errors – Event ID 304 and 307 (Microsoft 365).
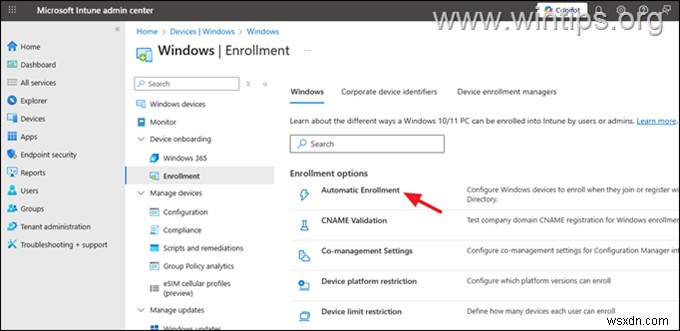
Step 1. Allow Auto Enrollment and Disable WIP on Microsoft Intune.
1. Navigate to Intune Admin Center > Devices > Windows > Enrollment and open Automatic Enrollment.
2. Here make the following changes to enable the Automatic MDM enrollment and click Save:
-
Set the MDM user scope to All to allow all users to enroll a device.
-
Set the Windows Information Protection (WIP) user scope to None.
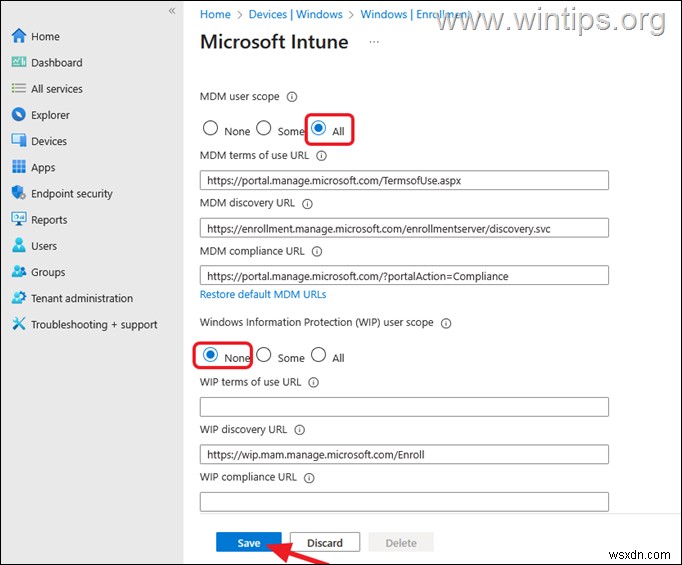
3. Wait a few minutes and then try again to register the device in Microsoft Entra.
Step 2. Enable Automatic MDM Enrollment using a Group Policy in Local AD
(HYBRID JOIN).
In order to be able to enroll on-premises domain devices in Intune, you must
allow the automatic MDM device enrolment for users via Group Policy. To do this:
1. Open the Group Policy Management Editor on your domain controller and navigate to:
- Computer Configuration > Administrative Templates > Windows Components > MDM
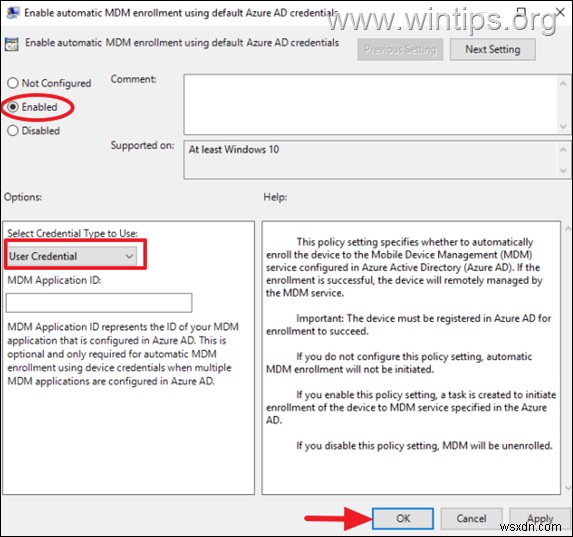
2. Open the Enable automatic MDM enrolment using default Azure AD credentials policy.*
* Note: If the "Enable automatic MDM enrolment using default Azure AD credentials" policy setting is not there, see the instructions on the following articles on how to add it.
- How to Automatically Enroll Active Directory devices in Intune using Group Policy.
- Enroll a Windows device automatically using Group Policy.
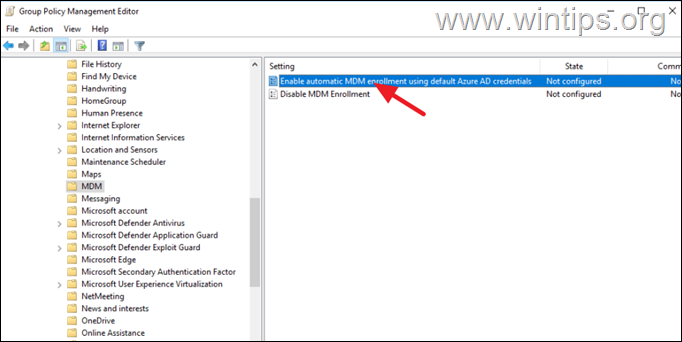
3. Set the policy to Enabled and below select User Credential as the credential type to use for enrollment.
4. Close Group Policy Editor and run the "gpupdate /force" command to apply the policy.
5. Try again to enroll the device in Entra/Intune by adding the user's Microsoft 365 account to the device.
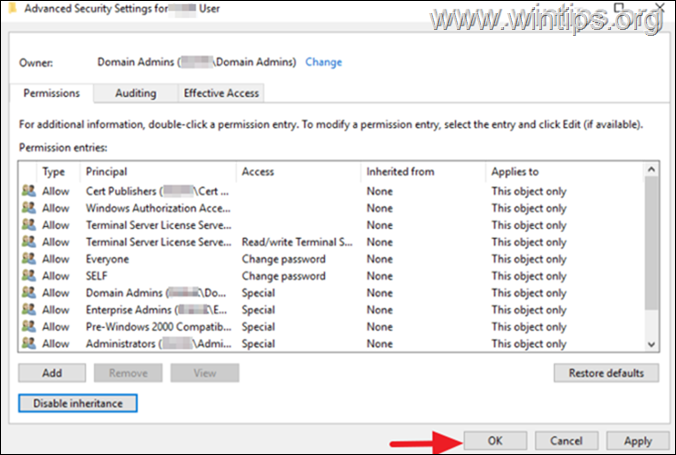
Step 3. Enable Permissions Inheritance on the Affected User Account.
If you're syncing your local AD to Microsoft Entra with the Azure AD connect tool and you receive the mentioned error, proceed and enable permissions inheritance on the domain user account that is trying to register their device with Microsoft Entra ID or enroll it in Intune.
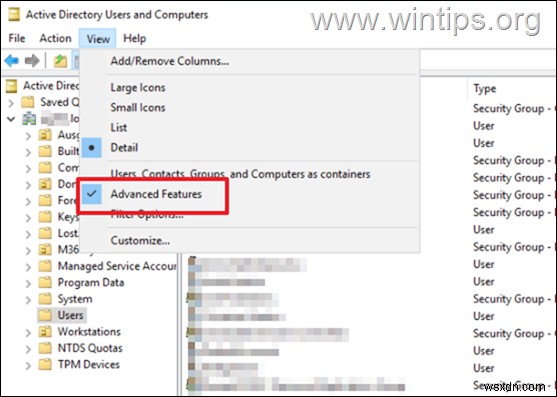
1. Open Active Directory Users and Computers.
2. On the View menu, enable the "Advanced Features" option.
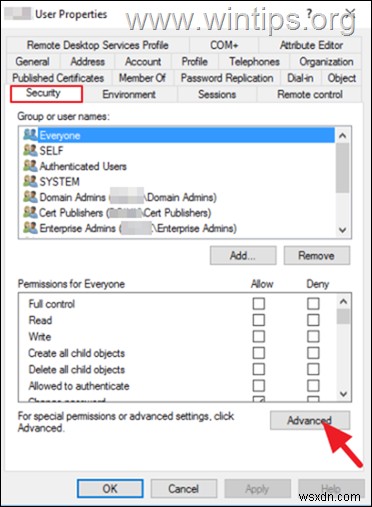
3. Then, right-click on the domain user who wants to join their device to Entra and open their Properties.
4. Navigate to Security tab and click Advanced.
5. On Permissions tab, click Enable inheritance.
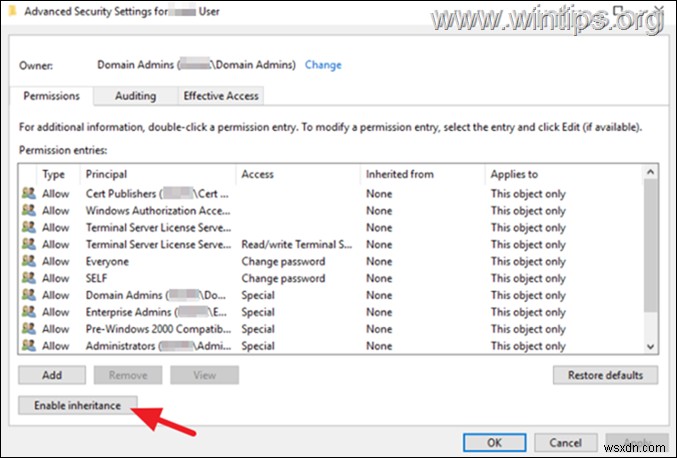
6. Click Apply > OK and then OK again to close the 'User Properties' window.
Additional help: If the mentioned problem occurs during the AD Connect synchronization, read the following article to grant the required permissions on the Azure AD Connect account:
- https://learn.microsoft.com/en-us/troubleshoot/entra/entra-id/user-prov-sync/troubleshoot-permission-issue-sync-service-manager#part-3-grant-the-missing-permissions
That's it! Let me know if this guide has helped you by leaving
your comment about your experience. Please like and share this guide to help
others.
Frequently Asked Questions
What is the cause of the 'Automatic registration failed at join phase' error in Microsoft Entra ID/Intune?
This error typically occurs when Intune Auto Device Enrollment is disabled, or the Azure AD login account lacks sufficient access rights for synchronization. It can also happen if domain users have incorrect rights for device registration/enrollment.
How can I fix the 'Automatic registration failed at join phase' error with Event IDs 304 and 307?
To fix these errors, enable Auto Enrollment in Intune, disable Windows Information Protection, use Group Policy to enable automatic MDM enrollment, and ensure permission inheritance on affected user accounts in Active Directory.
What changes are needed in Intune to resolve the 304 and 307 Event ID errors?
In the Intune Admin Center, set the MDM user scope to 'All' and the Windows Information Protection (WIP) user scope to 'None' under the Automatic Enrollment settings.
How do I enable automatic MDM enrollment using Group Policy for on-premise domain devices in Intune?
Access the Group Policy Management Editor, navigate to Computer Configuration > Administrative Templates > Windows Components > MDM, and enable the policy 'Enable automatic MDM enrollment using default Azure AD credentials', choosing 'User Credential' as the credential type.
If this article was useful for you, please consider supporting us by making a donation. Even $1 can a make a huge difference for us in our effort to continue to help others while keeping this site free:
- Author
- Recent Posts
Konstantinos is the founder and administrator of Wintips.org. Since 1995 he works and provides IT support as a computer and network expert to individuals and large companies. He is specialized in solving problems related to Windows or other Microsoft products (Windows Server, Office, Microsoft 365, etc.).
Latest posts by Konstantinos Tsoukalas (see all)
