
For several years a number of governments around the world have worked tirelessly to monitor or somehow regulate the way in which their citizens interact on the Internet. Due to services like Tor and virtual private networks (VPNs), this task has been getting difficult and will continue to do so for the foreseeable future. As long as there are people willing to make utilities that help people become anonymous on the Web, there will always be a way to work around regulations and blocks set up by centralized administrations.
Onion routing (through Tor) has been one of the most popular ways of accomplishing this. At the end of October developers released a new service that runs on top of Tor that allows for anonymous chat/messaging. Here’s a condensed run-down on what you should know about this service.
How It Works
If you’re unsure of how Tor works, I’ve already written a piece here on MTE that explains it. On top of Tor, the messenger system will work by connecting you through the OR protocol first, then adding your chat service of choice’s protocol as another layer on top of it. You can connect to Facebook, Jabber, IRC, Google Talk, Twitter, Yahoo, and many other services that allow for private conversations using this method. The goal of Tor Messenger is to allow conversations between people in countries where such a protocol is blocked for various reasons. You will always be able to find a Tor relay in a country where these services are not blocked, allowing you to both chat and hide your location with end-to-end encryption.
Can’t You Just Run Tor Through Your Favorite Application?
Here’s where we get to the crux of Tor Messenger and what makes it special compared to just configuring your application to run through Tor and using it to chat instead. Yes, technically you can configure onion routing through your browser, Yahoo! Messenger, or whatever it is you use to chat. But while that may give you peace of mind knowing you’re appearing from another country, it still allows exchanges and relays with your encryption keys to view the messages sent through their servers. The keys work only until the message is decrypted by the last server before reaching its destination.
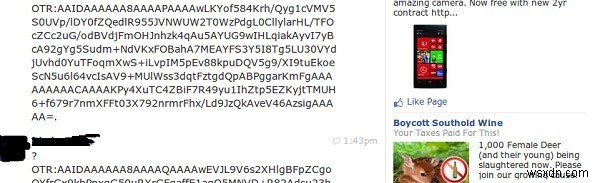
With Tor Messenger you have an added layer of functionality. Instead of having a traditional cryptography model, you will be using “Off-the-Record” (OTR) messaging. The way OTR works is that you and your friend on the other side decide on a secret key to use and input it directly into the messenger interface. Your messages will be decoded not by the server sending them but by the program running on your computer. This leaves every OR relay (even the one on the tail end of the transmission) completely clueless about what you’ve sent or received. By doing this you eliminate the possibility that your traffic will somehow be sniffed out by someone malicious. Instead, only you and the person on the other end will see the message itself rather than the gibberish that is normally transmitted through the web.
Can’t Someone See The Key Before It’s Used, Though?

Of course, if you exchange the key through the same messaging system you intend to use it in, you’ve technically made all this effort for nothing. Someone can just easily grab your key and decode the entire conversation anyway. My suggestion is to make a phone call, send an SMS (less safe), or meet in person to exchange the key with the person you intend to speak with. Use a different key for each person you speak with to eliminate every possibility of sabotage if the conversation is extremely sensitive.
As long as you adopt these good practices, you’ll be able to keep your head underwater if privacy is that important to you in those particular moments.
What do you think? Is Tor Messenger taking paranoia a little too far, or is it providing an essential service? Tell us in a comment!
