XINSTALL BY CLICKING THE DOWNLOAD FILE
Store BitLocker keys in Active Directory to simplify device recovery and keep encrypted drives manageable. This guide explains how to enable storage, verify key backups, and recover keys when needed.
Table of contents
- How Do I Store BitLocker keys in Active Directory?
- Configure Group Policy to store keys in AD
- Verify BitLocker keys in AD
- Recover a BitLocker key from AD
- Force existing devices to upload keys
- Check stored keys with PowerShell
- FAQ
How Do I Store BitLocker keys in Active Directory?
Configure Group Policy to store keys in AD
BitLocker only uploads recovery keys to Active Directory when the correct policy is active.
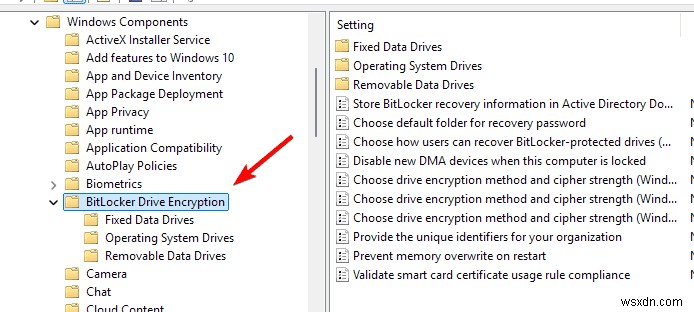
- Open the Group Policy Management Console on your domain controller.
- Go to Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption.
- Select Enabled.
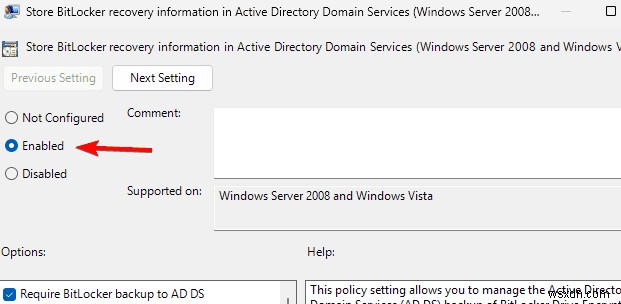
- Turn on Backup recovery passwords and key packages.
- Click Apply, then OK.
- Run gpupdate /force on client machines.
You can also read a detailed guide on how to unlock BitLocker without a password or recovery key if a device already locks itself.
Verify BitLocker keys in AD
Admins should confirm that BitLocker keys appear in Active Directory after encryption.
- Open Active Directory Users and Computers.
- Select View, then enable Advanced Features.
- Browse to the computer object.
- Right click it and choose Properties.
- Open the BitLocker Recovery tab.
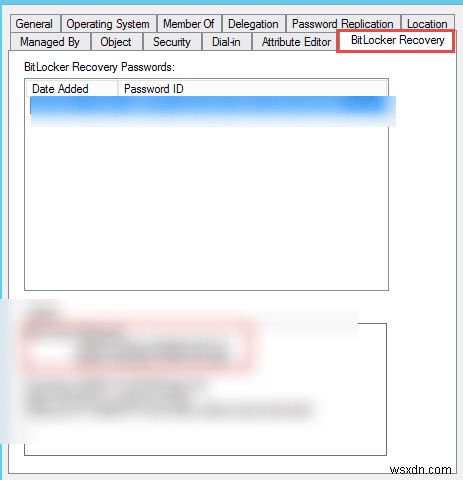
- Review the stored recovery password and key package.
You can also learn how to locate keys from the command line with this guide on getting the BitLocker recovery key from CMD.
Recover a BitLocker key from AD
When a device asks for the BitLocker recovery key during startup, you can pull it directly from Active Directory.
- Open Active Directory Users and Computers.
- Search for the locked computer.
- Open its Properties window.
- Click the BitLocker Recovery tab.
- Choose the correct recovery entry.
- Copy the 48 digit recovery key and enter it on the affected PC.
Force existing devices to upload keys
Older encrypted devices may not send keys to Active Directory until you trigger a backup.
- Run manage-bde -protectors -get C: in Command Prompt.
- Copy the Key Protector ID from the output.
- Run manage-bde -protectors -adbackup C: -id {ProtectorID}.
- Reopen the device entry in Active Directory to verify the new upload.
This process also helps when you follow steps from this guide on what to do if the Windows 11 BitLocker recovery key is lost.
Check stored keys with PowerShell
PowerShell lets you audit all BitLocker recovery objects stored in Active Directory.
- Open PowerShell as administrator.
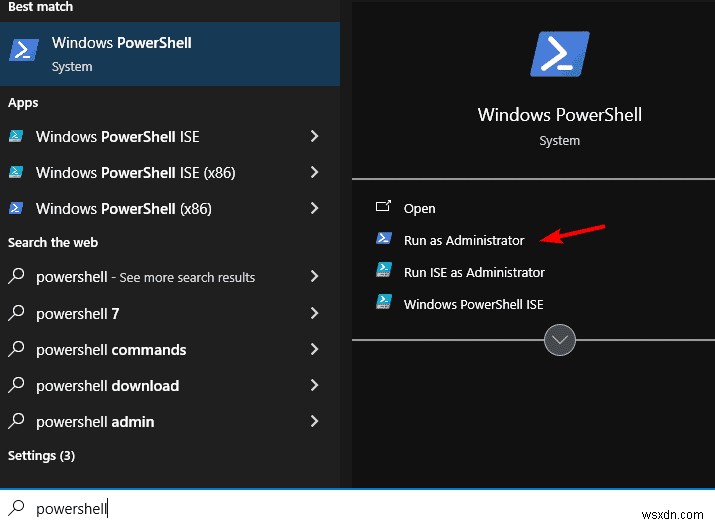
- Run:
Get-ADObject -Filter 'objectClass -eq "msFVE-RecoveryInformation"' -Properties msFVE-RecoveryPassword - Review the returned recovery objects for each device and confirm that keys match your records.
FAQ
Does BitLocker require Active Directory to store keys?
No. BitLocker can work with local key storage, but Active Directory gives you central control and easier recovery for domain devices.
Can I store TPM owner information in AD as well?
Yes. You can configure related Group Policy settings so Windows stores TPM owner information next to BitLocker data in Active Directory.
Do I need Windows Server for this to work?
Yes. You need Active Directory Domain Services on Windows Server or a compatible environment that manages domain joined computers.
Can Azure AD replace on premises AD for BitLocker keys?
Yes. Azure AD can store BitLocker recovery keys for Azure joined Windows devices and offers a cloud based way to retrieve them.
Active Directory storage for BitLocker keys keeps your encryption setup organized and secure. After you enable the Group Policy setting, confirm keys per device and test retrieval to avoid surprises during lockouts. This approach helps IT teams reduce downtime, protect data, and maintain a clear recovery process for every encrypted machine.
Milan Stanojevic
Windows Toubleshooting Expert
Milan has been enthusiastic about technology ever since his childhood days, and this led him to take interest in all PC-related technologies. He's a PC enthusiast and he spends most of his time learning about computers and technology. Before joining WindowsReport, he worked as a front-end web developer. Now, he's one of the Troubleshooting experts in our worldwide team, specializing in Windows errors & software issues.
Readers help support Windows Report. We may get a commission if you buy through our links.

Read our disclosure page to find out how can you help Windows Report sustain the editorial team. Read more
