Published Mar 10, 2026, 11:00 AM EDT
Oluwademilade is a tech enthusiast with over five years of writing experience. He joined the MUO team in 2022 and covers various topics, including consumer tech, iOS, Android, artificial intelligence, hardware, software, and cybersecurity. In addition to writing at MUO, his work has appeared on HowtoGeek, Cryptoknowmics, TechNerdiness, and SlashGear.
Oluwademilade attended the University of Ibadan in Nigeria, earning a medical degree from the College of Medicine. Excelling in public service, Oluwademilade was honored with the title of Global Action Ambassador by a student organization affiliated with the United Nations. He received this designation in Kuala Lumpur, Malaysia, in recognition of his efforts to make a positive global impact in 2020
In his free time, Oluwademilade enjoys testing new AI apps and features, troubleshooting tech problems for family and friends, learning new coding languages, and traveling to new places whenever possible.
You probably assume that if something shady happens on your PC, your antivirus will catch it. And maybe it will — eventually. But by the time traditional security software raises a flag, the damage can already be done. What if your computer could keep a detailed, running journal of everything happening under the hood: every process that launches, every network connection that opens, every time a file's creation timestamp gets suspiciously altered?
That's exactly what Sysmon does. It's a free, Microsoft-built tool that belongs to a broader category of Windows Sysinternals tools for catching suspicious behavior. The interesting part is that even though these utilities are the gold standard for finding spyware and adware on your PC, most everyday Windows users may have never heard of them.
Sysmon gives Windows a level of visibility that its built-in logging can't match
Event Viewer was never going to cut it
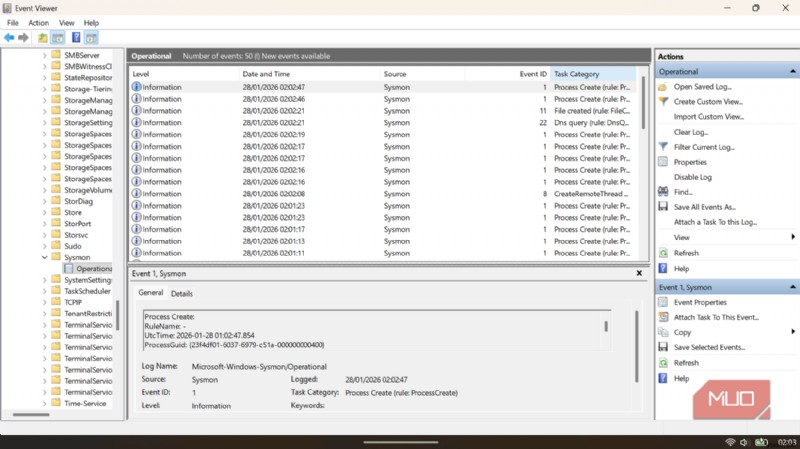
Windows already keeps event logs, and if you’ve ever opened Event Viewer to troubleshoot issues, you’ve probably noticed how chaotic they can feel. There’s a lot of noise and not always enough clarity. Sysmon, short for System Monitor, is a different animal entirely. Once installed, it runs as a persistent system service and device driver, surviving reboots, and writes richly detailed events to the Windows event log. The difference is similar to comparing a grainy security camera with one capable of reading license plates.
Sysmon's event catalog logs process creation along with the full command-line arguments, so you don’t just see that a program ran, you see how it was launched. It also records network connections, including the originating process, IP address, port, and hostname. That makes it possible to trace which application contacted which server and when. It even flags changes to file creation timestamps, a classic trick malware uses to disguise itself as legitimate system files. Beyond that, Sysmon keeps an eye on driver loading, registry changes, DNS queries, and more advanced techniques like process hollowing, logged under Event ID 25, where malicious code hides inside an otherwise essential Windows process.
 Related
Related
This is how to tell if your PC is silently being used for something else
Think your PC might be doing more than you asked? Here’s how I check for hidden activity.
Here's a draft table covering the most security-relevant event IDs:
Event ID
Name
What It Captures
1
Process Create
Every process that launches, including the full command line, parent process, and file hash. It's the single most useful event for spotting suspicious executions.
2
File Creation Time Changed
Flags when a process deliberately alters a file's creation timestamp, a classic malware tactic to blend in with legitimate system files.
3
Network Connection
Logs outbound TCP/UDP connections, linking each one to the process that made it. It is essential for detecting beaconing or data exfiltration.
6
Driver Loaded
Records kernel drivers as they load, including signature status. Unsigned or unexpected drivers are a serious red flag.
7
Image Loaded
Tracks DLLs loading into processes; disabled by default due to volume, but powerful for detecting DLL hijacking when filtered carefully
8
Create Remote Thread
Detects when one process injects a thread into another, which is a hallmark technique of code injection and process hollowing attacks.
10
Process Access
Fires when one process opens another's memory, catching credential theft tools targeting LSASS (the process that stores Windows login secrets).
11
File Create
Logs new files created or overwritten, particularly useful when watching Temp, Downloads, and Startup folders.
12–14
Registry Events
Covers registry key creation, deletion, value changes, and renames, the primary way malware establishes persistence across reboots.
15
File Create Stream Hash
Catches files downloaded via browser by logging the Zone Identifier stream attached to them. It's useful for tracing the origin of suspicious executables.
17–18
Pipe Events
Monitors named pipe creation and connections, a common inter-process communication method used by malware and post-exploitation frameworks like Cobalt Strike.
19–21
WMI Events
Tracks WMI filter and consumer registration, a favored fileless persistence technique that leaves almost no trace without this event.
22
DNS Query
Logs every DNS lookup a process makes, making it possible to spot connections to known malicious domains even before a full TCP connection is established.
25
Process Tampering
Detects process hollowing and herpaderping (techniques that replace legitimate process memory with malicious code to evade detection).
29
File Executable Detected
Flags the creation of any new executable (PE format) file on the system, a strong early indicator of a dropper or installer running.
This is how to get Sysmon up and running
If you can open a terminal, you're already most of the way there
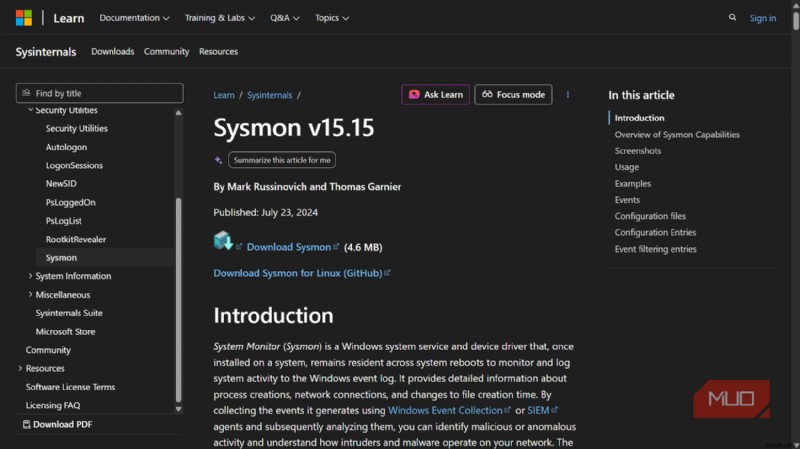
Sysmon is a free download from Microsoft's Sysinternals page (version 15.15 as of this writing), and installation is a single command. You'll need administrator privileges and a brief detour through PowerShell or the Command Prompt, but the whole process takes under five minutes.

Sysmon
OS Windows (with a Linux version also available)
Developer Microsoft (Sysinternals team)
Price model Free
Sysmon is an advanced system monitoring tool that logs detailed Windows activity, such as process launches, network connections, and file changes. It runs in the background, giving security pros deep visibility into what’s happening inside a PC.
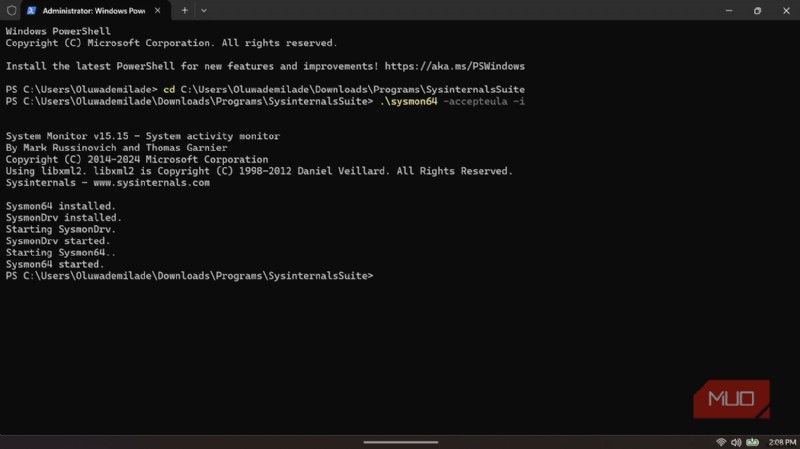
Head to the official Sysmon page on Microsoft Learn, download the ZIP file (around 4.6MB), and extract its contents. Then open PowerShell or Command Prompt as an administrator, navigate to the folder, and run:
.\sysmon64 -accepteula -i
That's the basic install: Sysmon will install its service and driver in the background. In fact, you don't even need to reboot. From that point forward, it begins logging events to Applications and Services Logs -> Microsoft -> Windows -> Sysmon -> Operational in Event Viewer. You can view those logs immediately.
Uninstalling is just as simple: sysmon64 -u. The tool never tries to entrench itself, which I respect.
You don't have to figure this out alone
The default Sysmon installation is functional, but it really comes into its own with a configuration file. Sysmon accepts an XML config that specifies which events to log, which to filter out, and how granular to go. If you aren't familiar with the format, you can brush up on what an XML file is and how to use it, as these files define the "logic" Sysmon uses to monitor your system. Writing your own from scratch is a project — but you don't have to.
The cybersecurity community has produced some outstanding ready-made configs. The most widely used is the SwiftOnSecurity sysmon-config, available free on GitHub, with nearly 5,000 stars and over 1,700 forks. It's been carefully tuned to capture security-relevant events while filtering out the noise that would otherwise make your logs unreadable. Every line is commented, so it doubles as a tutorial. To install with this config, you'd run:
sysmon64 -accepteula -i sysmonconfig-export.xml
To update an existing installation with a new config file:
sysmon64 -c sysmonconfig-export.xml
If you want something even more modular, the sysmon-modular project by Olaf Hartong (on GitHub) offers a composable, community-maintained approach that maps directly to the MITRE ATT&CK framework. Both are excellent starting points.
It won't stop every attack, but you'll know one happened
You don't need to be a security engineer to run Sysmon well. You need a decent config file, a willingness to open Event Viewer occasionally, and the satisfaction of knowing that if something strange ever happens on your machine, you'll have a record of it. That peace of mind, to me, is well worth five minutes of setup.
